threat modelingagents
Threat modeling stalls in shift-left workflows because intent-based interfaces run into an articulation barrier. Staged delegation inside the engineer's editor, backed by specialist agents and a graph-native model, is one resolution.
April 20, 202631 min read
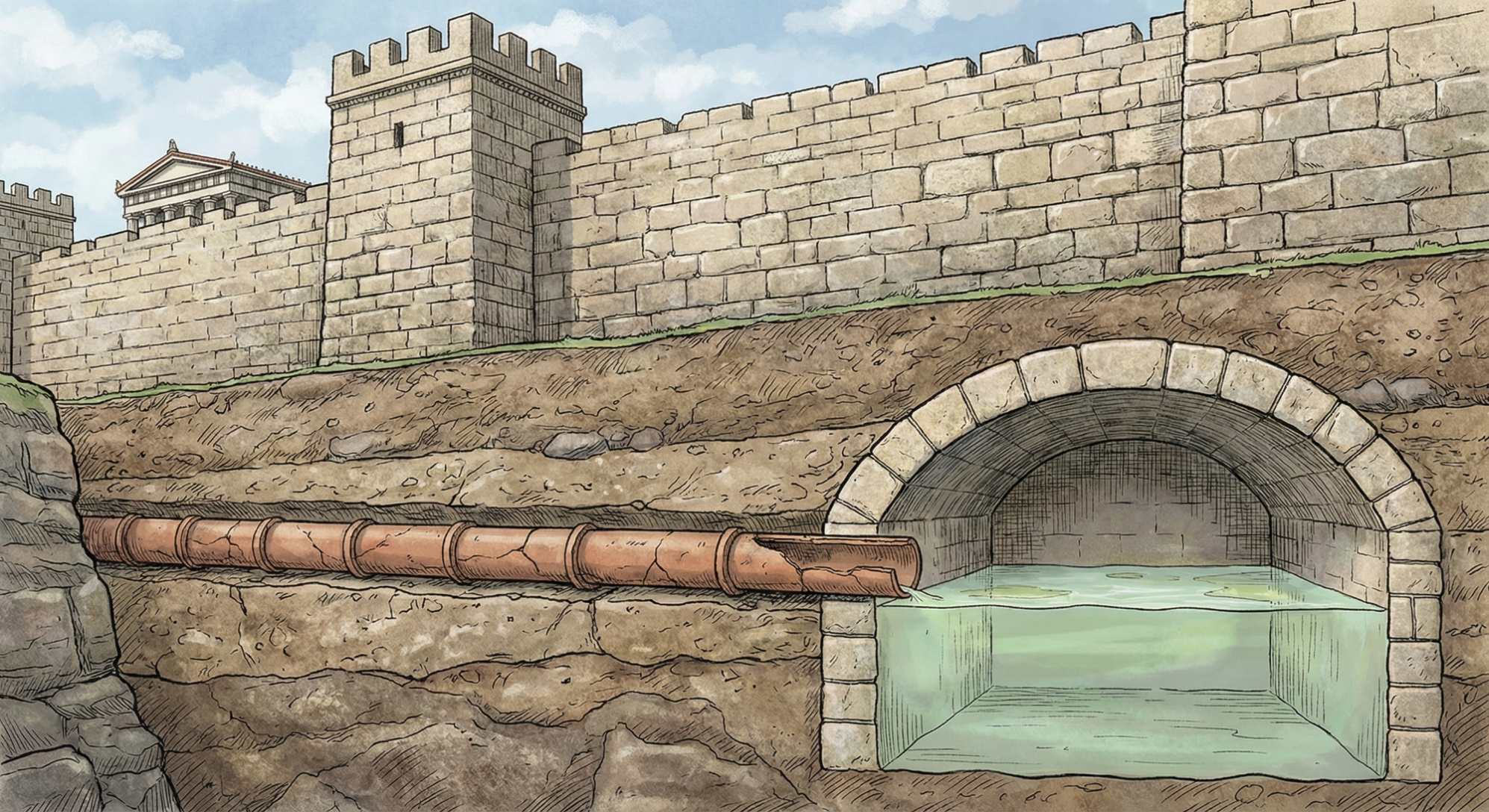
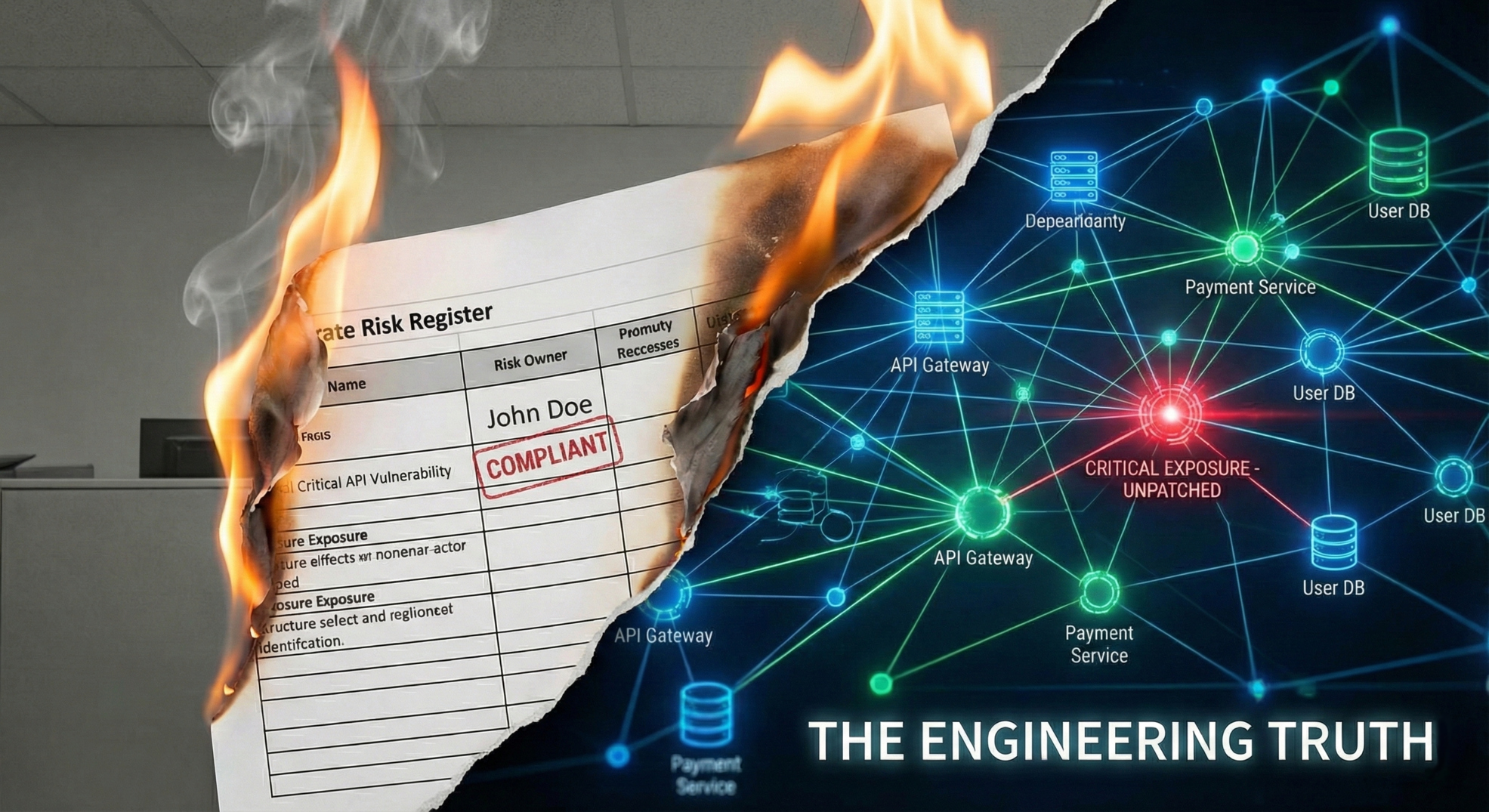
compliancesecurity architecture
The Kingdom of Complia defended its castle with the finest compliance framework the medieval world had ever produced. The enemy walked around the back.
March 22, 20268 min read
threat modelinggraph theory
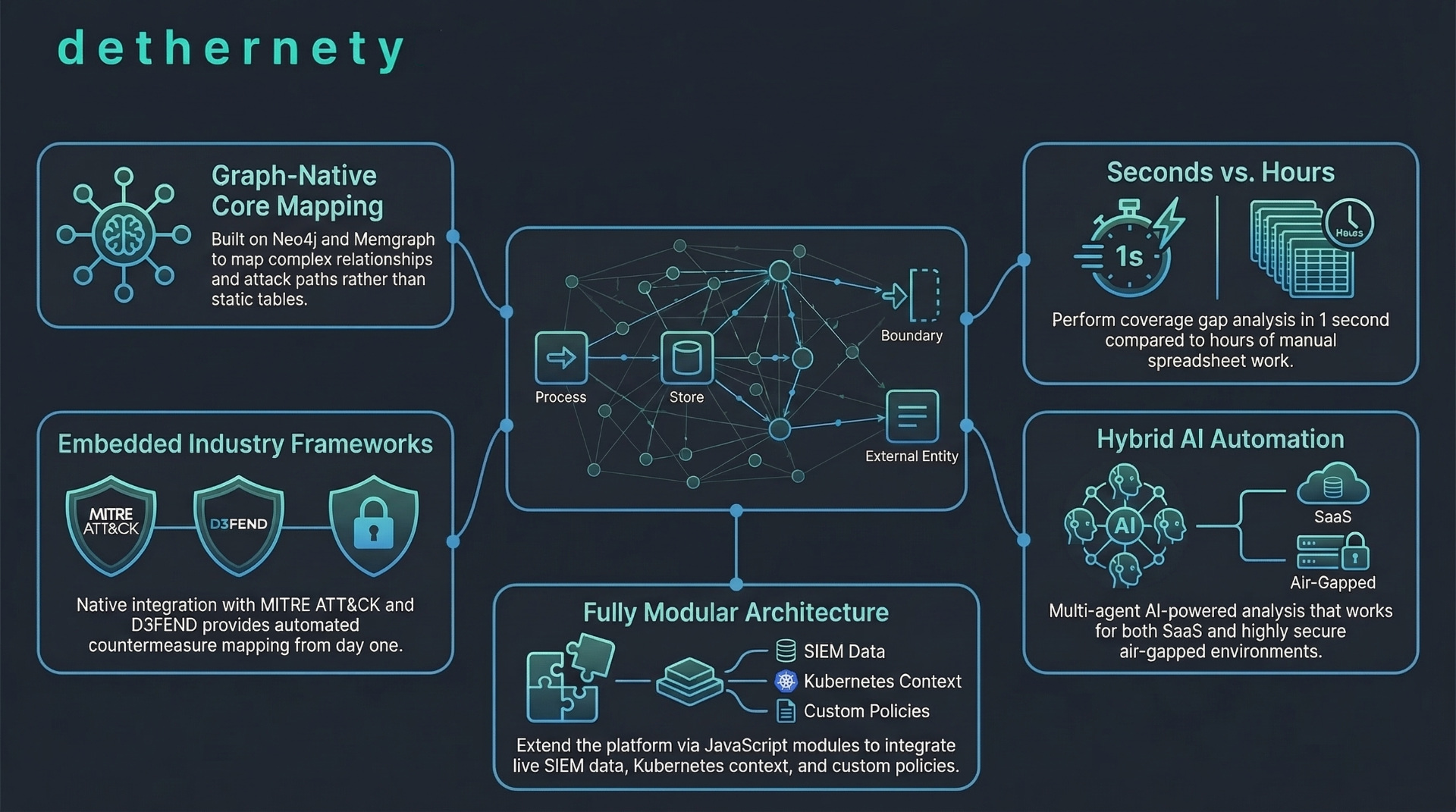
A 20-minute podcast covering Dethernety's graph-native architecture, MITRE ATT&CK integration, hybrid AI tiers, and how the platform secures its own infrastructure.
March 11, 20265 min read
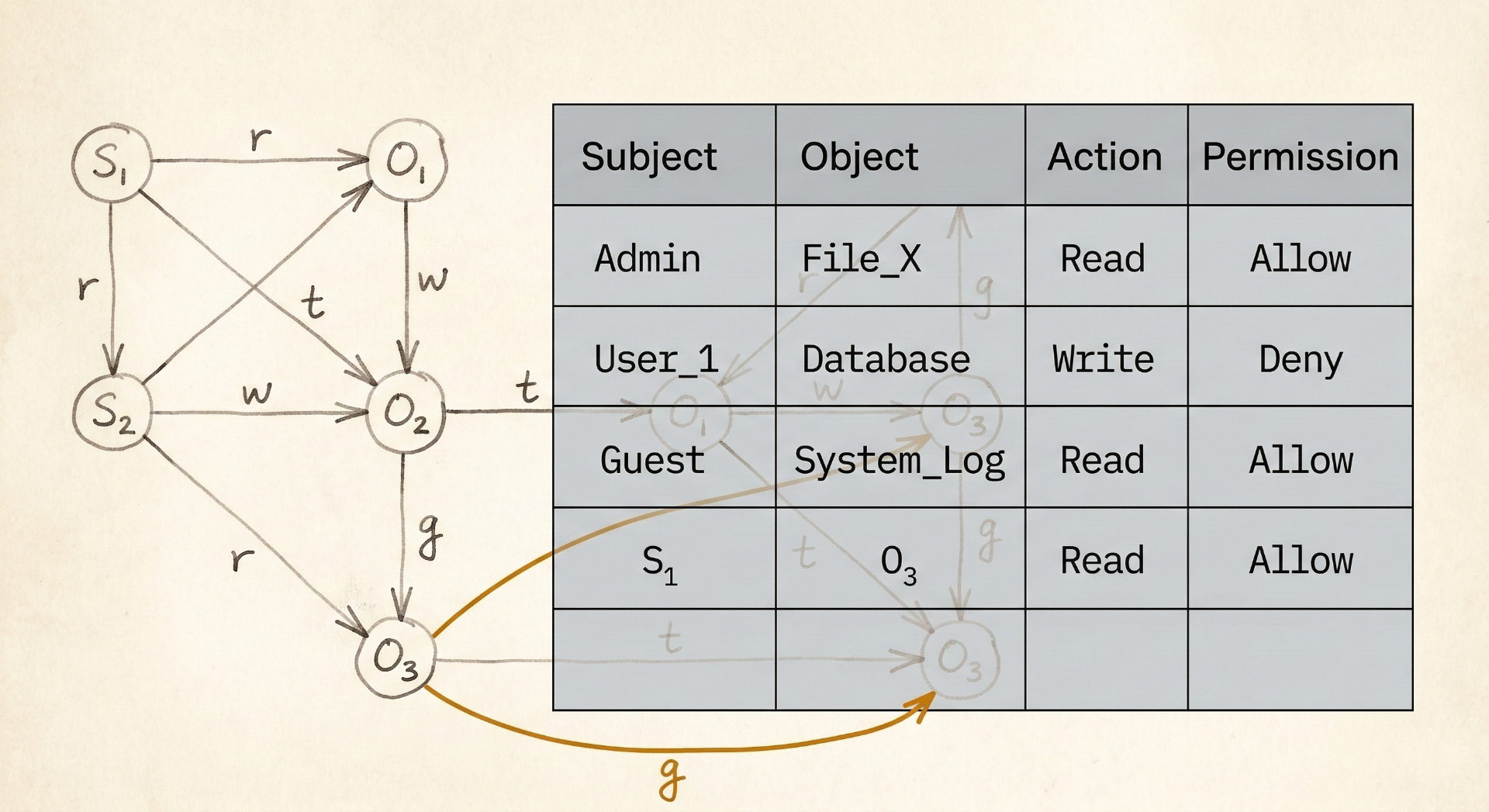
graph theoryaccess control
In the 1970s, we proved security is a graph problem. Then we abandoned the math for flat ACLs. Now graph databases let us pick it back up.
March 9, 202612 min read
vulnerability managementrisk prioritization
The Three Mile Island operators were drowning in alerts when they shut off the emergency cooling. Your platform team is drowning in CVEs. Both problems have the same root cause — and the nuclear industry solved it decades ago.
March 4, 20269 min read
threat intelligencegraph theory
Most SOCs consume threat intel feeds but lack the contextual infrastructure to make them actionable. Drawing on the mRNA vaccine analogy, this article argues that graph-native environment models are the missing regulatory network your indicators depend on.
March 2, 20269 min read
AWSFedora CoreOS
How an immutable OS with a read-only root filesystem and Podman quadlets replaces both configuration management and container orchestrators on a single-node deployment.
February 25, 202617 min read
AWSCloudFront
CloudFront VPC Origins eliminate public IPs and load balancers, but introduce three engineering problems — TLS provisioning, WebSocket limitations, and a volume attachment deadlock — that don't exist with traditional architectures.
February 24, 202616 min read
AWSself-service
How the self-service management plane provisions per-customer infrastructure through gated stages, without introducing shared paths that undermine the isolation model.
February 23, 202616 min read
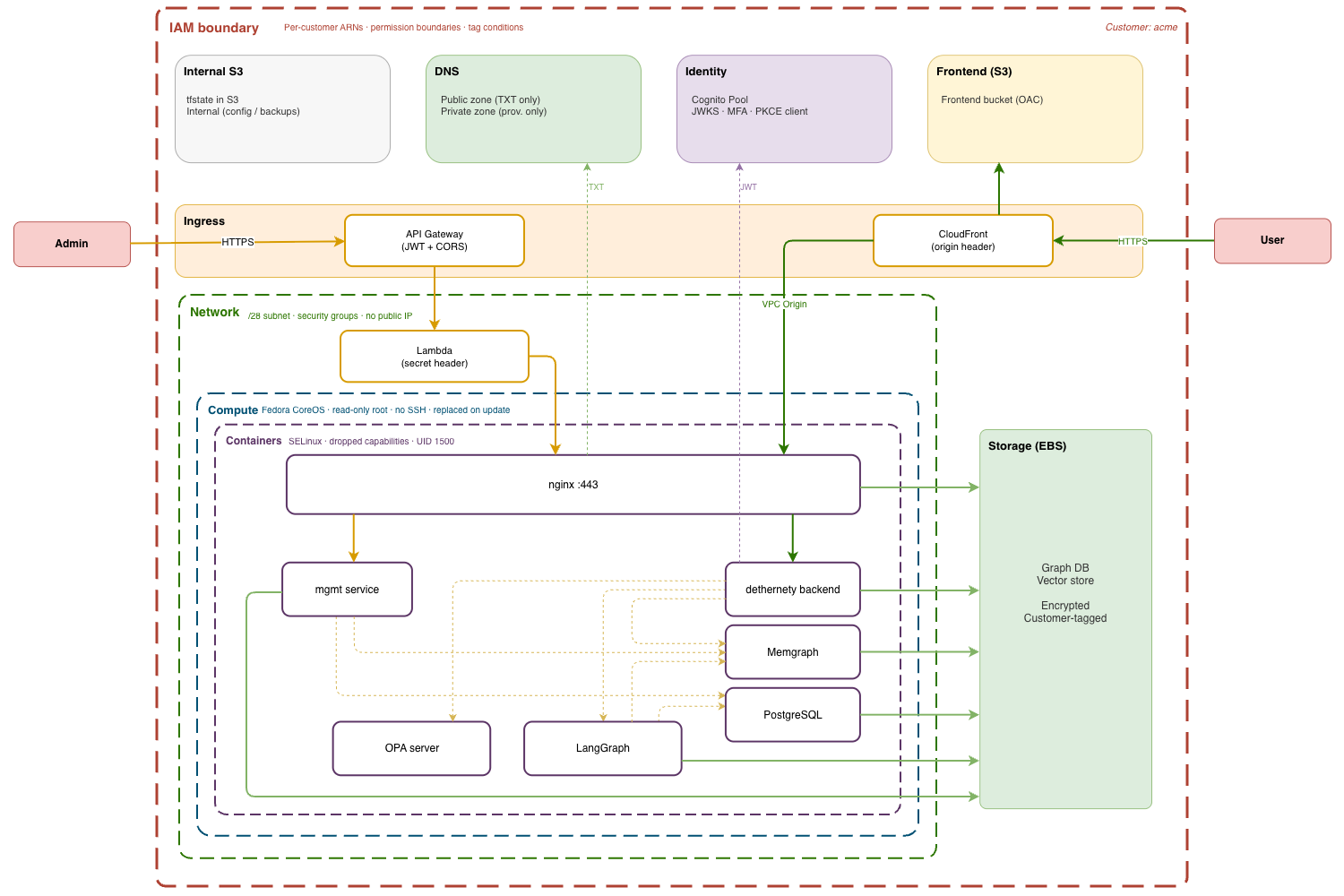
AWSIAM
How per-customer blast radius containment works across layers of AWS infrastructure — IAM, network, DNS, identity, storage, state, compute, and ingress — each enforcing isolation on its own.
February 22, 202614 min read
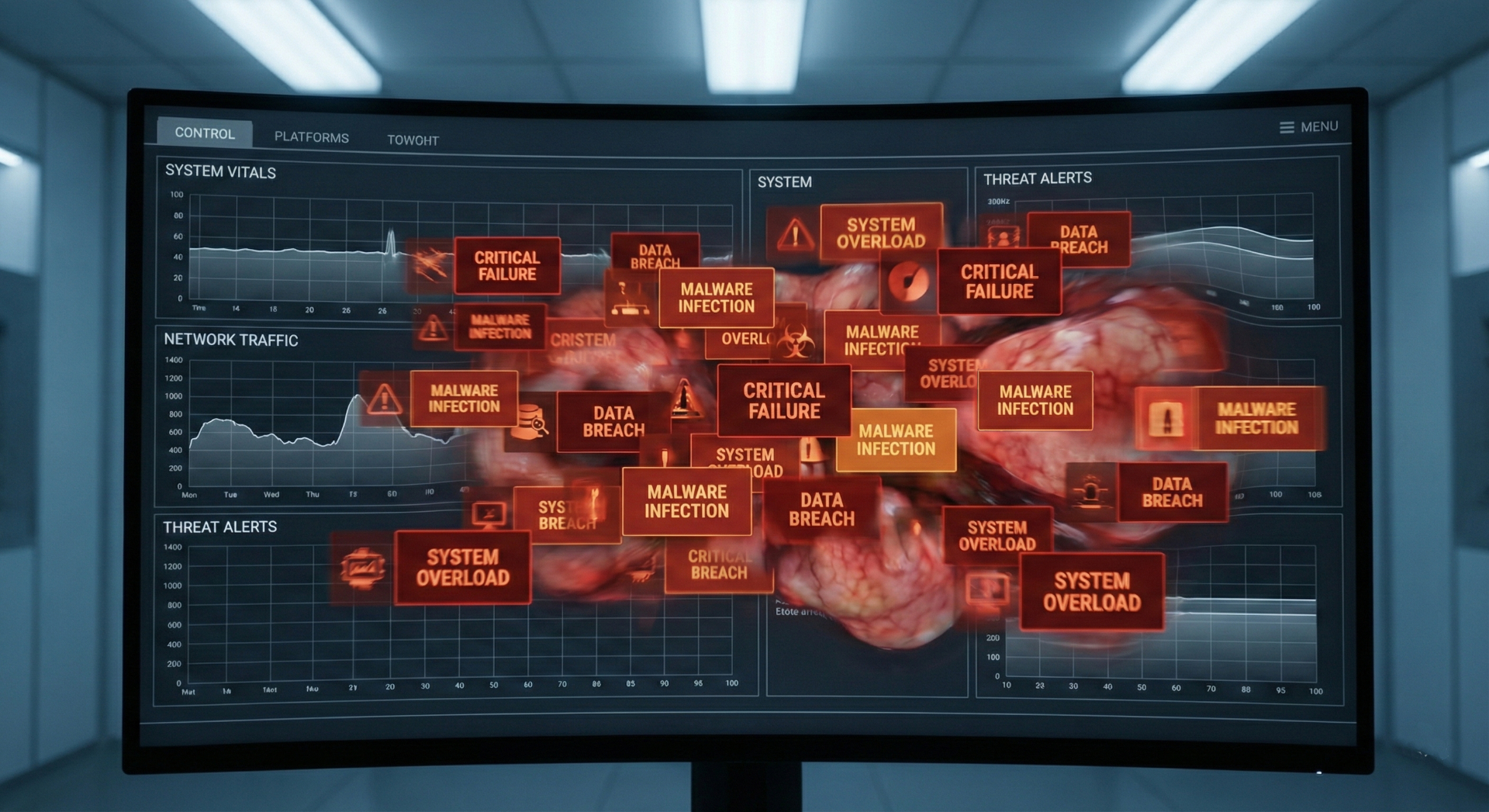
siemsoar
The average SOC gets 4,484 alerts per day and ignores most of them. That's autoimmune disease, not a detection gap. How Jerne's Immune Network Theory maps onto graph-based architectures that suppress noise instead of generating more of it.
February 21, 202611 min read
AWSmulti-tenant
Per-customer infrastructure isolation on AWS, where a cross-tenant breach means handing an attacker the blueprint to an organization's defenses.
February 20, 202613 min read
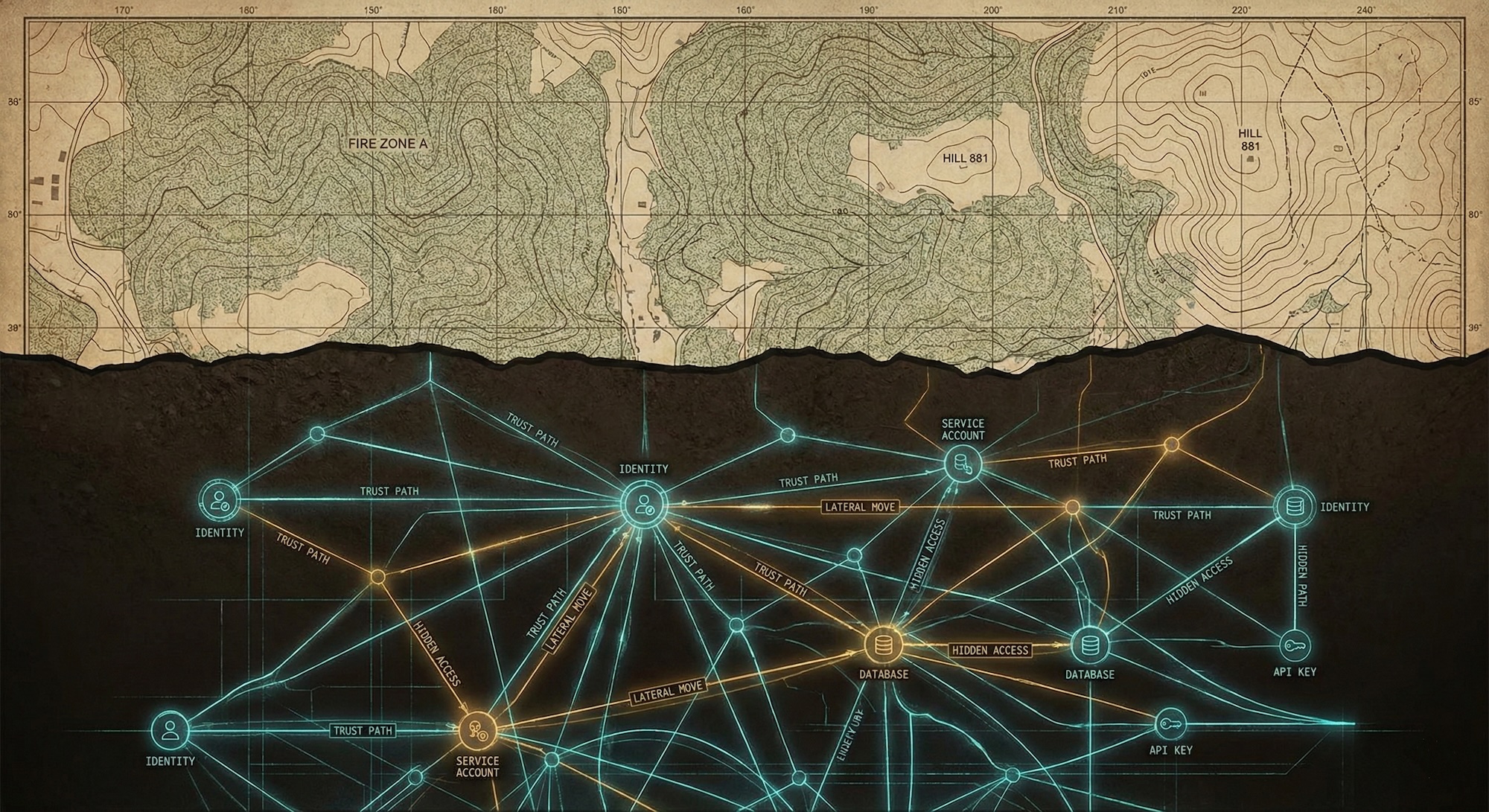
supply chainmarginal analysis
From the siege of Kirrha to SolarWinds, attackers bypass walls by compromising what's already trusted. Why authentication proves provenance but not intent, and how to allocate scarce verification budget across a dependency graph you'll never fully see.
February 13, 202613 min read
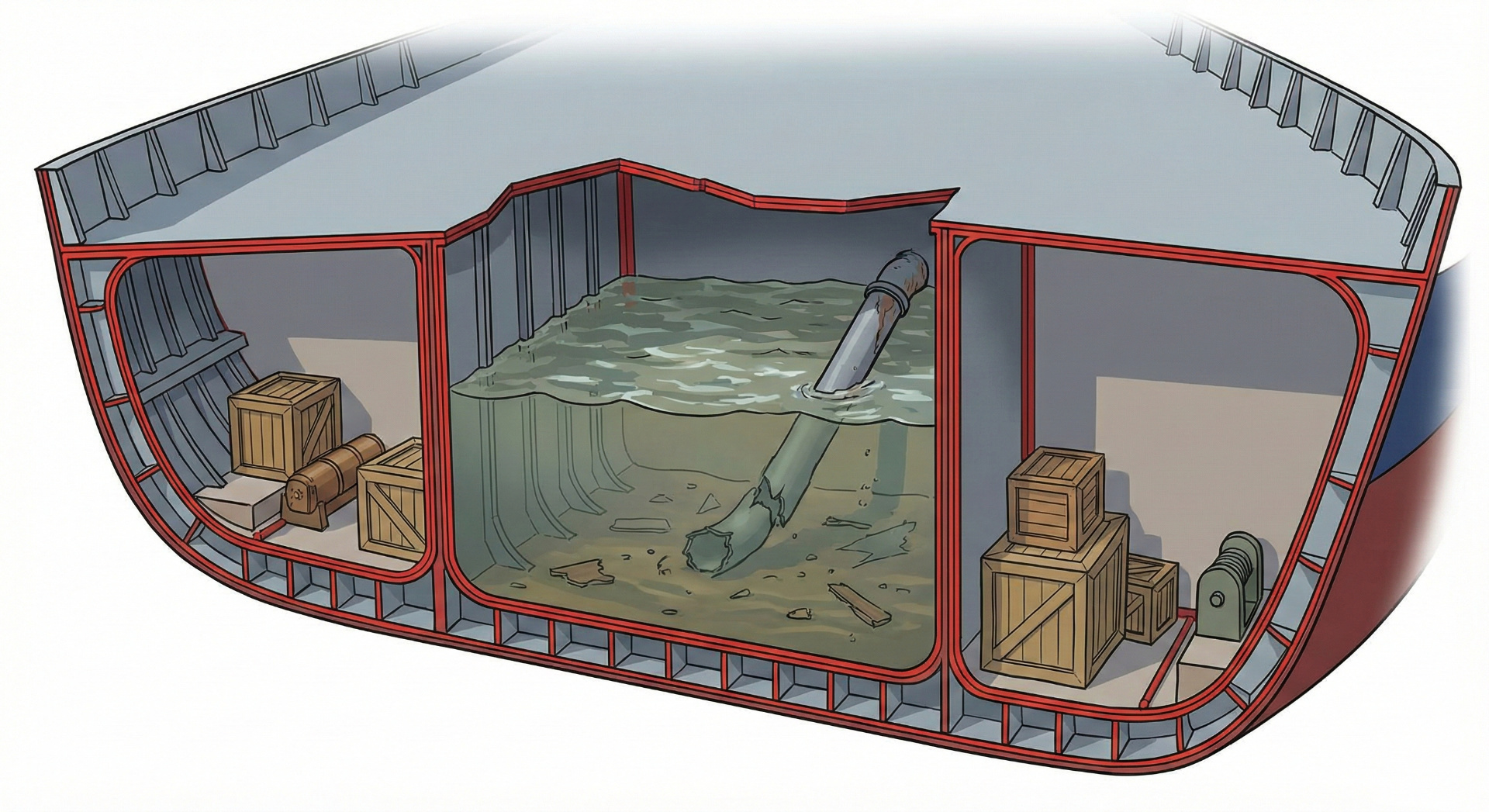
graph theorysecurity architecture
The Củ Chi tunnels were 250 kilometers of passages dug with shovels. The US had satellites. The tunnels worked because they exploited topology, not topography. Attackers still do.
February 4, 20267 min read
zero trustnetwork security
The firewall-first mindset creates fragile networks that collapse on breach. Designing firewall-last forces you to build self-defending nodes, prune unnecessary connections, and treat the perimeter as defense in depth—not a structural dependency.
February 2, 20269 min read
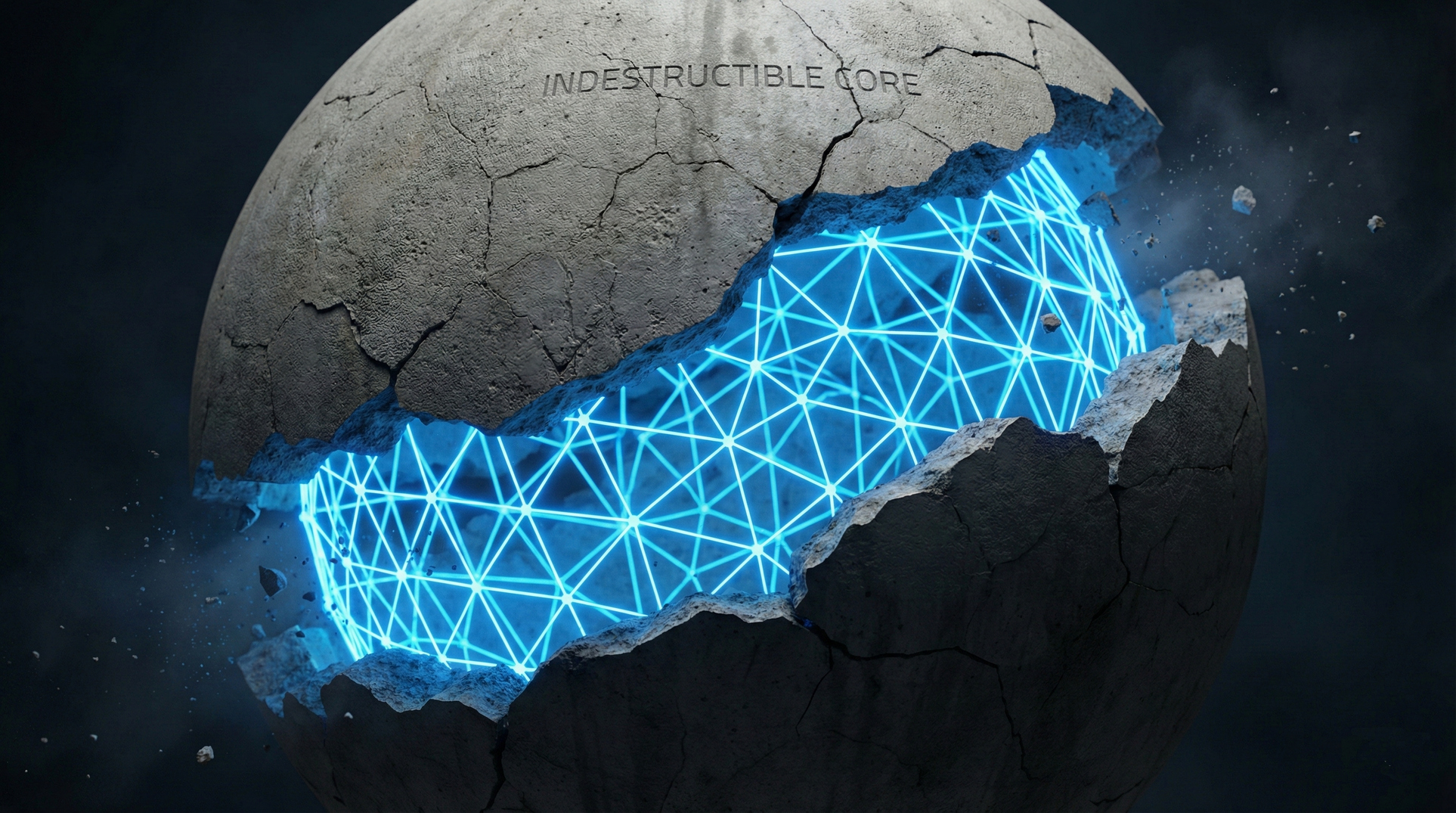
zero trustgraph theory
Every vendor is selling Zero Trust. None of them are selling graph databases. That's the problem. You can't determine 'necessary edges' without mapping your current graph—and no identity proxy solves that.
January 23, 20267 min read
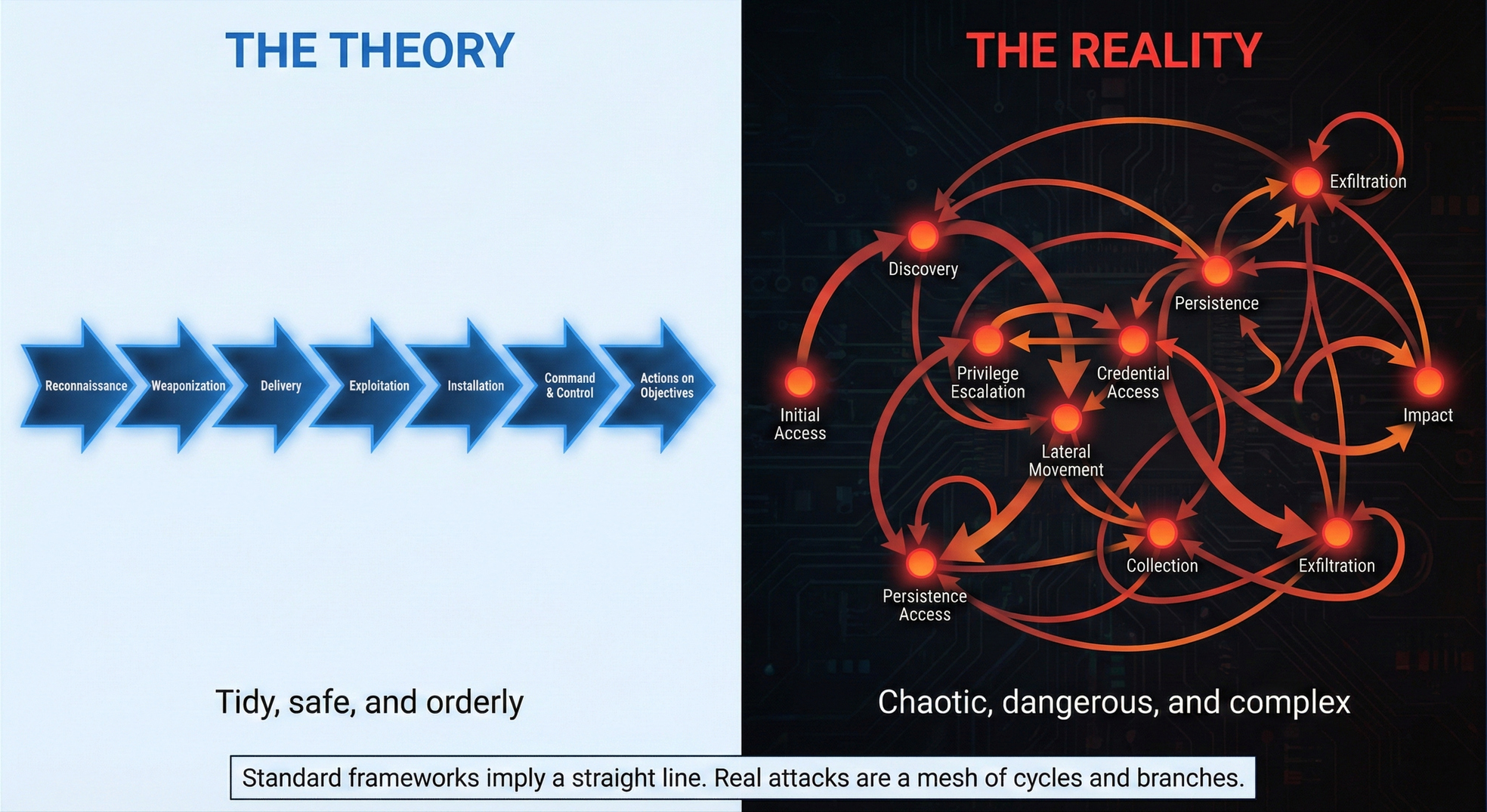
threat modelingattack modeling
The Kill Chain shows attacks as linear progressions. Real attacks loop through lateral movement, branch based on what they find, and restart tactics on every new system. Graph theory models what linear frameworks can't.
January 12, 202610 min read
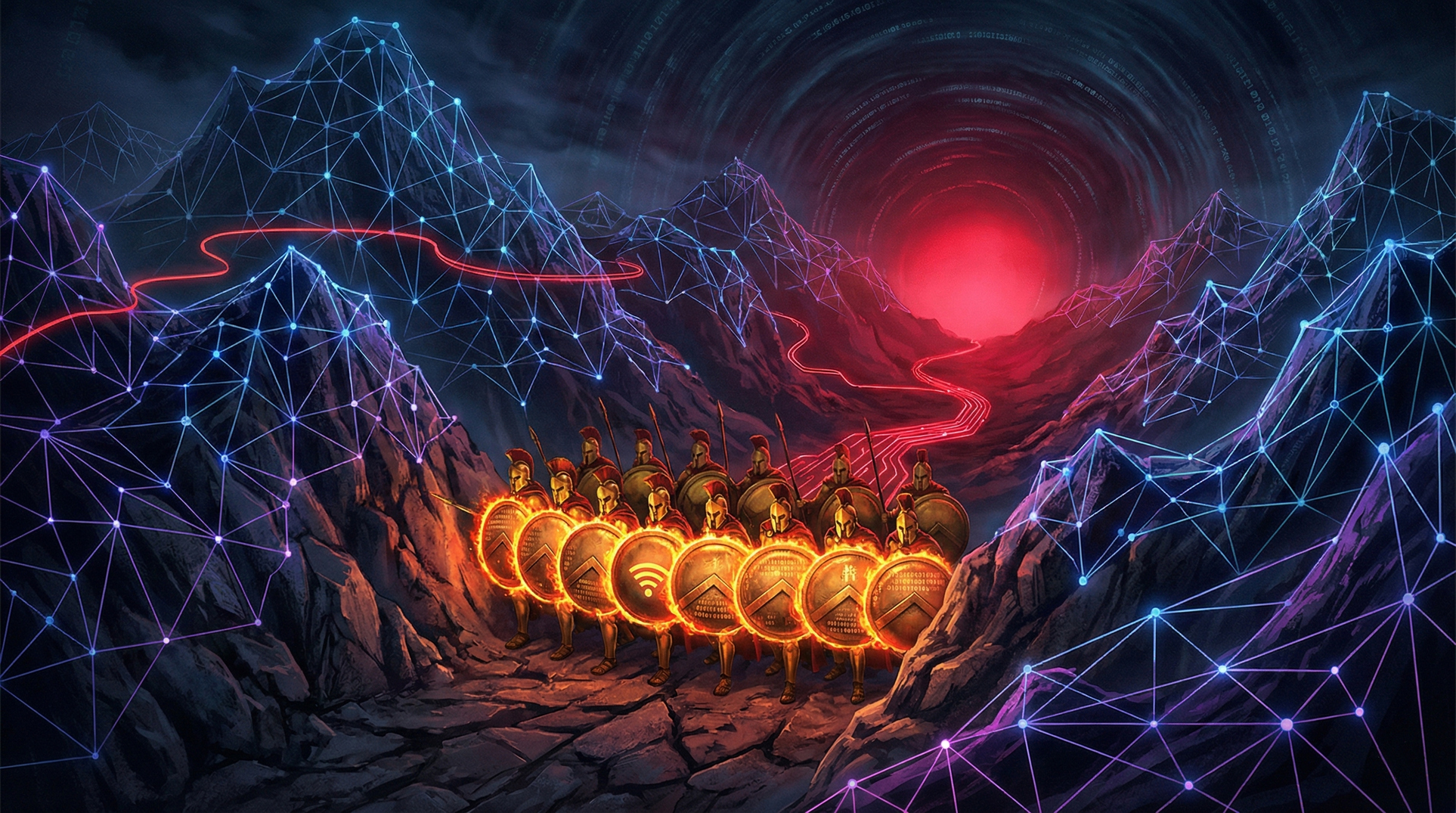
graph theoryperimeter security
The Spartans built the perfect defensive chokepoint—and were destroyed by a path they didn't know existed. Graph theory reveals why perimeter security fails and what modern defenders must do instead
January 8, 202611 min read
graph theorysecurity architecture
You cannot optimize what you cannot measure. Security teams ask graph theory questions—attack paths, blast radius, chokepoints—but use tools built for lists. Here's why that gap is costing you.
December 29, 20258 min read
risk managementorganizational design
Risk owner' sounds like a real role, but it's often just a name in a cell. True responsibility requires personal stakes: authority to act, accountability for outcomes, and capability to execute. Here's how to move from documentation to action.
December 17, 202512 min read
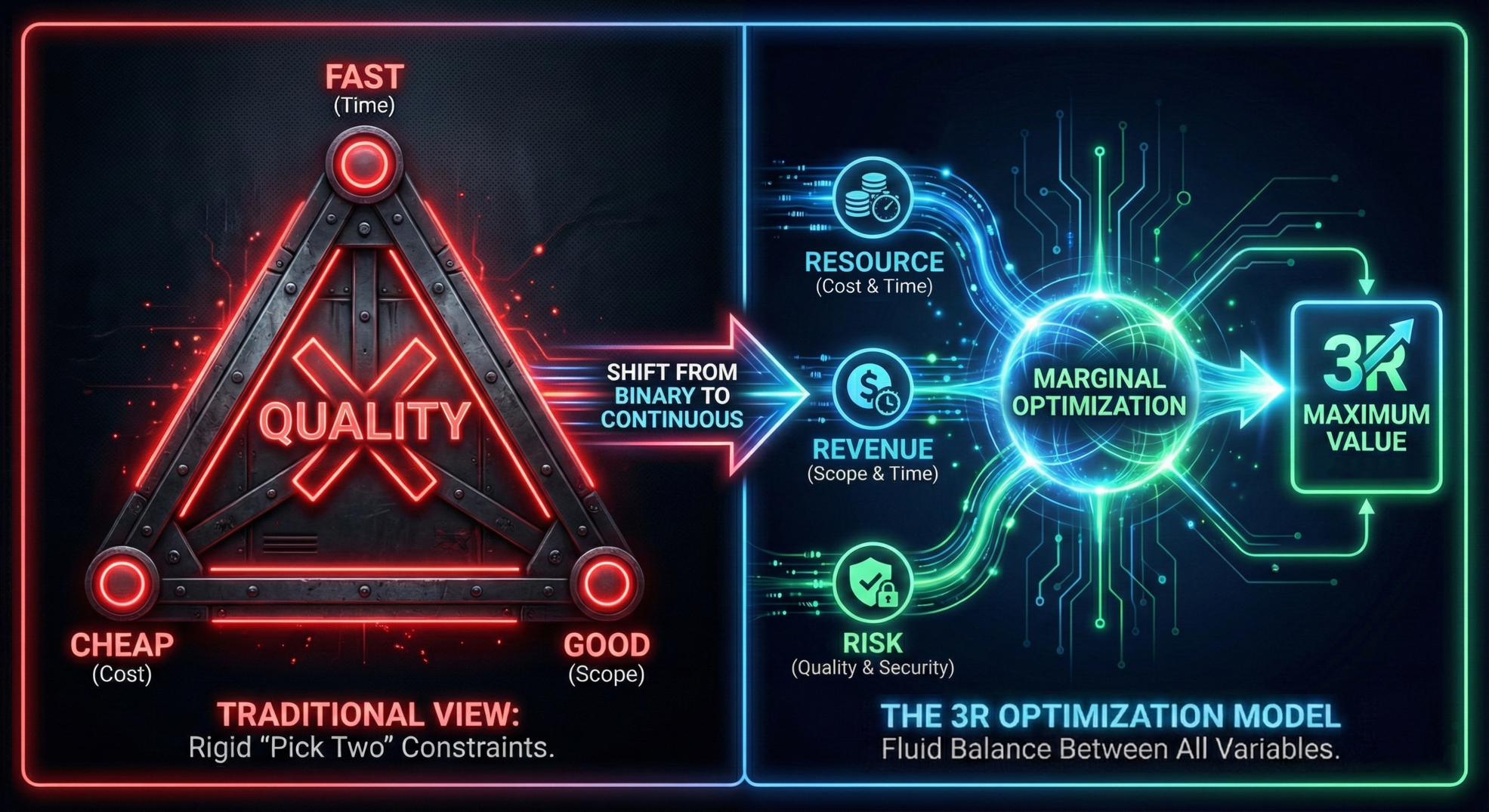
project managementeconomics
The Iron Triang le gives teams a convenient excuse for failure. The 3R Optimization Model—Revenue, Resources, Risk—forces them to do the math. Here's why marginal analysis beats binary trade-offs.
September 27, 20259 min read
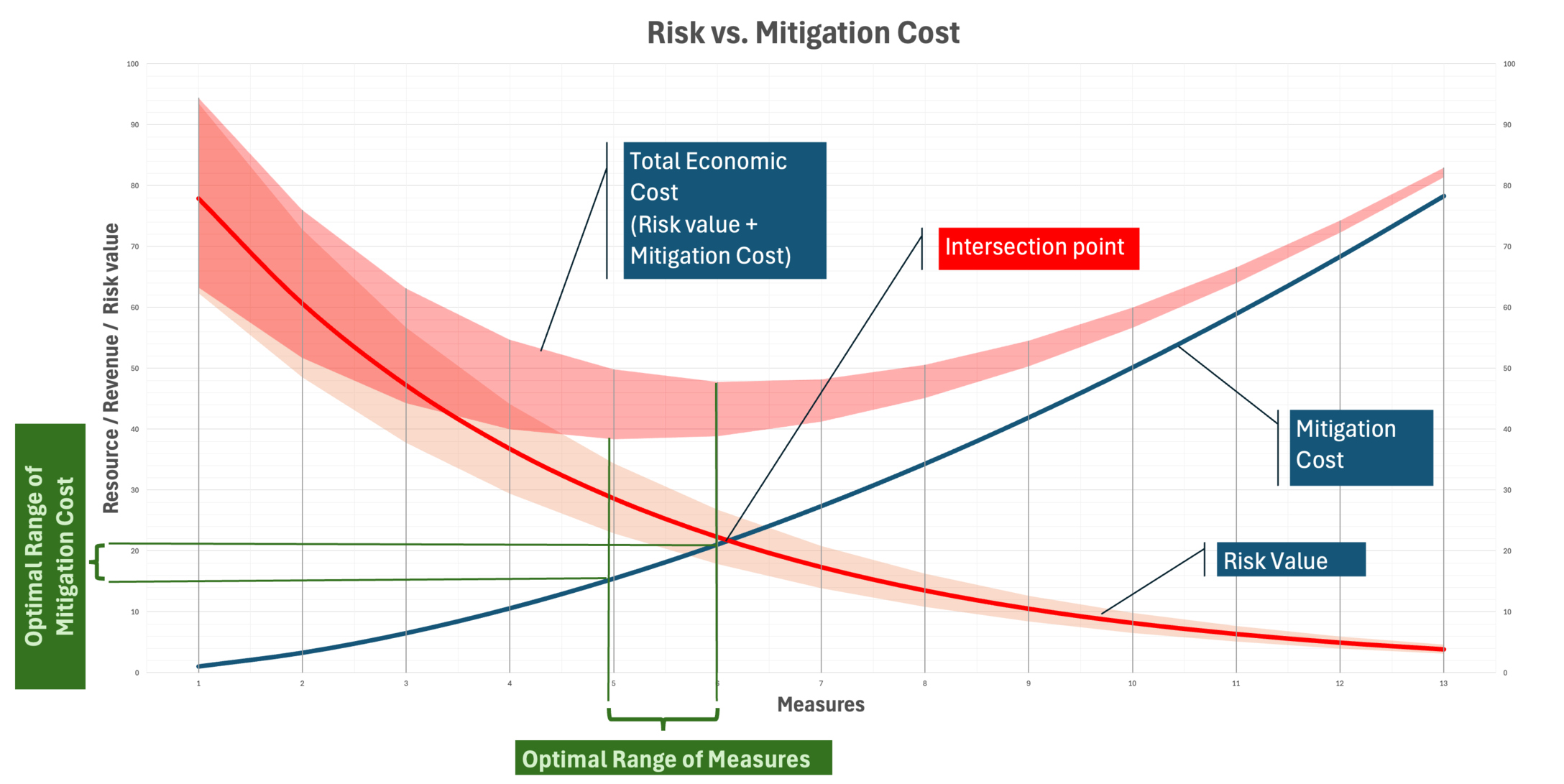
risk managementeconomics
The optimal security investment isn't where cost equals risk. It's where the next dollar spent reduces risk by exactly one dollar. Most articles get this wrong.
September 27, 20255 min read