Dethernety Podcast: Threat Modeling is a Graph Problem
AI-generated podcast. Listen to the full episode using the audio player above.
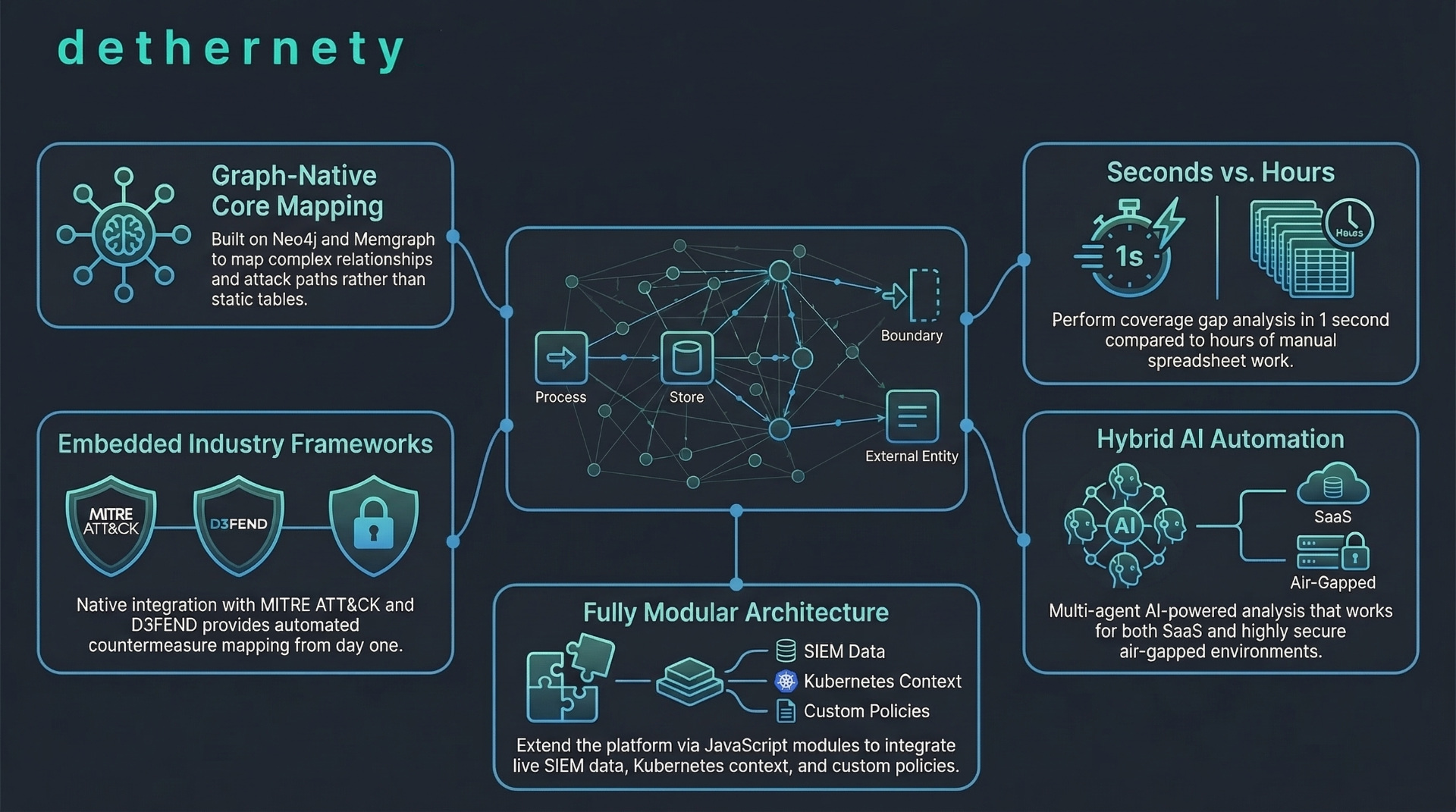
Most threat modeling still happens in spreadsheets and relational databases built for inventory tracking, not attack path analysis. This episode breaks down why that's an architectural mismatch and what a graph-native alternative looks like in practice.
This is the transcript of an AI-generated podcast episode about the Dethernety platform. The podcast is available as an audio player on the article page. The content below is a normalized summary of what the two podcast hosts discuss in the episode.
CORE ARGUMENT: THREAT MODELING IS A GRAPH PROBLEM
Traditional security tools use relational databases. For business logic like payroll or inventory, relational databases work fine. But in cyber security, the relationships between components matter more than the components themselves.
An attacker starts at a public-facing web server, finds a vulnerability, moves laterally through a firewall, exploits an internal API, and exfiltrates data from a customer database. Mapping that path across relational tables requires SQL JOIN operations that become clunky and resource-heavy with highly interconnected data. A ten-hop attack path in SQL is called "join hell" in the industry.
GRAPH-NATIVE ARCHITECTURE
Dethernety uses graph databases (Neo4j, Memgraph) instead of relational databases. Data exists as nodes (entities like servers, users) and edges (relationships between them). Relationships are stored physically on disk as first-class citizens, not computed at query time.
Scalability concern: graph databases historically had scaling issues, but modern graph databases are optimized for traversing connections at large scale.
Code comparison: tracing a multi-hop attacker path through a corporate network requires about 150 lines of recursive SQL. In Cypher (graph query language), the same result takes about 10 lines. That is 90% less code.
Analogy: using a relational database for threat modeling is like understanding a family tree by reading a spreadsheet where names are linked by ID numbers across 10 tabs. A graph database is like looking at the visual family tree directly.
WHY CONTEXT MATTERS
Attackers traverse relationships. They find a misconfigured server, steal an admin credential, use it to bypass an internal firewall. Security tools that analyze components in isolation miss the attack path. The context itself is the vulnerability.
MITRE FRAMEWORK INTEGRATION
Dethernety integrates MITRE ATT&CK (catalog of known adversary tactics and techniques) and MITRE D3FEND (catalog of defensive countermeasures).
Traditional workflow: an engineer manually cross-references a spreadsheet of servers against a MITRE PDF, guessing which techniques apply to which server.
Dethernety workflow: a system component automatically links to an exposure, which links to an ATT&CK technique. Example: a web server flagged as missing TLS encryption generates an exposure node mapped to the MITRE technique for transmitted data manipulation.
The defensive side works the same way: a component links to a control, which links to a countermeasure, which maps to a D3FEND technique. A network firewall maps to the MITRE technique for network traffic filtering.
GAP ANALYSIS
With this architecture, you can run a one-second query: "show me all ATT&CK techniques in our network that have zero defensive controls." This replaces days of manual spreadsheet cross-referencing for audit preparation.
MODULE ECOSYSTEM
Dethernety uses JavaScript packages as native platform extensions (not superficial webhook integrations). Three types of module classes:
- Design classes: extend the elements you can model. Example: a module adding Kubernetes components that pull live security context from a cloud API.
- Analysis classes: extend how you analyze the graph.
- Issue classes: allow bi-directional syncing with external trackers like JIRA or GitHub.
HYBRID AI ANALYSIS APPROACH
Three tiers of analysis:
Tier 1 — No AI (air-gapped/query-based): for organizations with strict data sovereignty, defense contracts, or compliance requirements. Uses deterministic Cypher or GraphQL queries only. Fully predictable and audit-ready. No sensitive data leaves the environment.
Tier 2 — Simple AI: a single LLM for everyday tasks like writing threat descriptions or recommending security controls for a specific node.
Tier 3 — Multi-agent AI: uses orchestrators like LangGraph or CrewAI. Multiple specialized AI agents collaborate — one acts as a security architect, another as an attacker, a third as a compliance officer. They analyze the graph, debate the blueprint, and produce a detailed threat report. Can generate custom interactive dashboards using Vue.js.
DETHERNETY STUDIO
A built-in AI agent that generates production-ready JavaScript module classes from natural language prompts. Instead of waiting months for a vendor to support a new cloud service, teams describe the component they need and the AI writes the integration code.
USER INTERFACES
All interfaces read from the same graph and MITRE integrations:
GUI: visual interactive canvas for security teams and architects. Drag-and-drop components, draw data flows, review auto-generated exposures in real time.
CLI: command-line interface for DevOps teams. Automates threat modeling as code in CI/CD pipelines. Every code push triggers an automatic threat model update based on the delta from the last version. This is shift-left security — identifying threats during the build phase.
MCP (Model Context Protocol): allows AI agents (like Claude Code) to interact directly with the threat model. An AI agent can discover infrastructure, import data or screenshots, and map architecture into the graph autonomously.
PLATFORM SECURITY
Dethernety's own infrastructure uses three layers of defense:
- Blast radius isolation: dedicated siloed resources per customer with strict IAM. A compromise of one customer environment cannot spread to another at the network level.
- Immutable infrastructure: runs on a stripped-down container-optimized OS. No patching allowed. Instead of patching (which causes configuration drift over time), containers are torn down and replaced with newly built secure versions. This is a "replace, don't repair" philosophy that guarantees a known-good state.
- Zero trust access: triple request validation, cryptographic measures to prevent DNS hijacking, strict isolation of internal routing.
FORWARD-LOOKING QUESTION
If MCP allows AI agents to read and comprehend an entire corporate infrastructure graph in milliseconds, how long until those agents are not just identifying threats but actively redesigning and deploying self-healing architectures without human intervention?